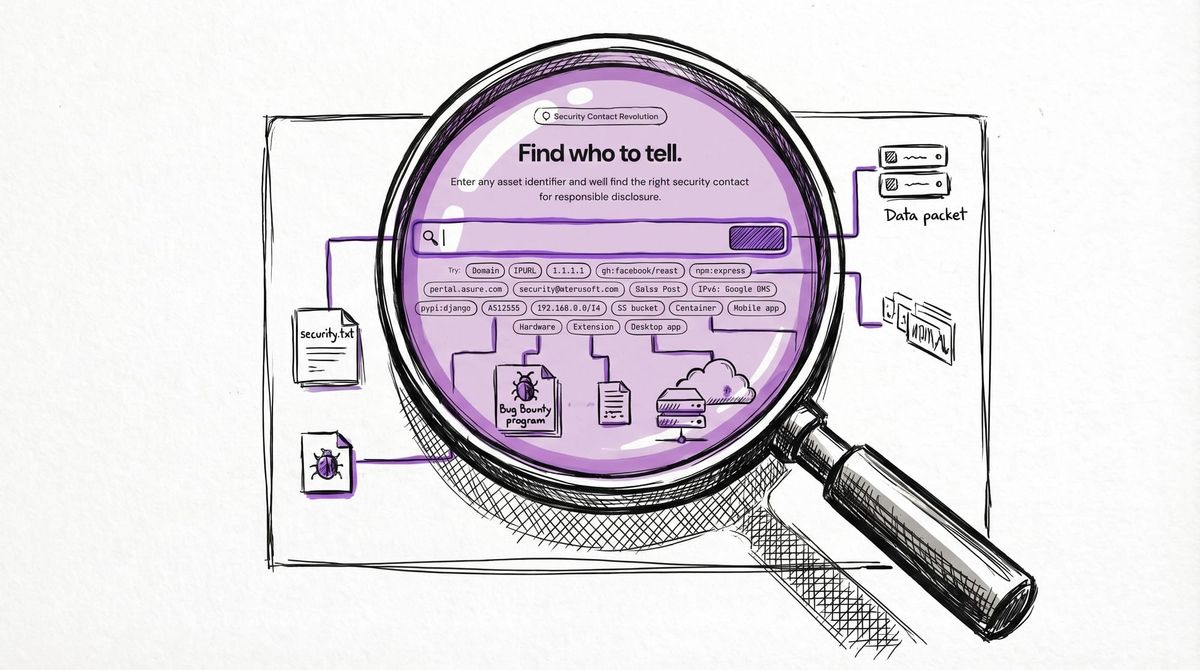
Introducing lookup.disclose.io: One Tool to Find All Security Contacts (Now in Beta)
Announcing lookup.disclose.io beta: universal security contact lookup for any digital asset. Find bug bounty programs, security.txt, and VDP contacts instantly.
Finding the right security contact shouldn't feel like a treasure hunt.
If you've ever tried to report a vulnerability, you know the frustration: Is there a bug bounty program? Where's the security.txt file? Should I email security@? Who even owns this system? What if it's a third-party package, or a cloud resource, or a mobile app?
Today, we're excited to announce the beta release of lookup.disclose.io — a universal security attribution tool that solves this problem once and for all.
The Problem: Security Contact Discovery is Broken
Every security researcher has been there. You find a vulnerability and want to do the right thing by reporting it responsibly. But first, you need to figure out where to report it. The current process looks something like this:
- Check for security.txt (maybe it exists, maybe not)
- Look for bug bounty program listings (scattered across platforms)
- Try convention emails like
security@domain.com(hope they're monitored) - Dig through WHOIS data (good luck parsing that)
- Search the web for "Company X vulnerability disclosure" (and pray)
- Give up and tweet about it (not ideal)
This fragmented, manual process wastes researcher time, delays disclosure, and sometimes prevents reporting altogether. Organizations lose out on valuable security intelligence, and the entire vulnerability disclosure ecosystem suffers.
The Solution: Universal Security Attribution
lookup.disclose.io takes any digital asset — a domain, IP address, package, repository, mobile app, hardware device, or organization name — and automatically finds all available security reporting channels, ranked by confidence and reliability.
What Makes It Different
Cross-Strategy Chaining: Unlike tools that only check one data source, lookup.disclose.io follows the relationships between assets. Start with an npm package? It finds the GitHub repository, extracts the organization domain, checks for security.txt, and looks up bug bounty programs. One input, complete attribution.
16 Input Types Supported:
- Traditional assets: domains, IPs, URLs, email addresses
- Modern assets: npm packages, Docker containers, GitHub repos
- Mobile and hardware:
app:WhatsApp,hw:Cisco ASA 5505 - Organization lookup: company names as fallback
Comprehensive Data Sources: The tool queries 22 different data sources including:
- disclose.io Database (2,400+ programs)
- security.txt (RFC 9116 specification)
- DNS Security TXT (draft standard developed by disclose.io)
- Bug bounty platforms (HackerOne, Bugcrowd, etc.)
- Package registries (npm, PyPI, Maven, etc.)
- WHOIS/RDAP data
- Corporate structure databases
- National CERT contacts (34 countries as backstop)
Confidence-Based Ranking: Results are sorted by reliability, with verified bug bounty programs and security.txt contacts at the top, convention emails and fallbacks at the bottom.
Key Features
Web Interface & CLI
- Web UI: Clean, dark-mode interface at lookup.disclose.io
- CLI tool:
bun cli.ts cloudflare.com --jsonfor automation - API endpoint:
POST /api/lookupfor integration
AI Agent Integration (Beta)
The tool includes an MCP (Model Context Protocol) server that exposes security contact lookup as a tool for AI agents and Claude Code. MCP was created by Anthropic and is now stewarded by the Linux Foundation as an open standard. This enables intelligent vulnerability disclosure workflows where AI can automatically identify the right contacts before helping draft disclosure reports.
Available MCP tools:
lookup_security_contact: Full security attribution lookupclassify_asset: Instant asset type classification
Example Workflows
Package Vulnerability: npm:express → npm registry → GitHub repository → expressjs organization → corporate structure → bug bounty programs
IP Address Investigation: 8.8.8.8 → RDAP lookup → Google attribution → Google VRP program + security.txt + abuse contacts
Mobile App Security: app:WhatsApp → Apple/Google platform contacts → Meta organization → Bug bounty program
Architecture: Built for Reliability
The tool uses a Strategy Pattern with parallel execution and intelligent chaining:
- Input Classification: Auto-detect asset type (or use prefixes like
npm:,gh:,app:) - Strategy Selection: Each asset type maps to a specialized strategy
- Parallel Execution: Multiple data sources queried simultaneously
- Chain Following: Results trigger additional lookups (up to 3 levels deep)
- Result Consolidation: Contacts deduplicated and ranked by confidence
Cycle detection prevents infinite loops, universal backstops ensure you always get at least national CERT contacts, and graceful degradation means the tool works even when individual data sources fail.
This is Open Source
lookup.disclose.io is built with the same open-source, vendor-agnostic principles as all disclose.io projects:
- License: MIT
- Runtime: Bun + TypeScript (no framework dependencies)
- Tests: 43 tests covering classification and engine logic
The project includes comprehensive data sources (data/certs.json, dioDB integration) and is designed for community contributions.
Beta Status: We Need Your Feedback
lookup.disclose.io is currently in public beta. The core functionality is stable and tested, but we're actively seeking feedback from the security research community to refine the tool before the 1.0 release.
What we're particularly interested in:
- Missing data sources: What security contact discovery methods are we missing?
- False positives/negatives: Cases where the tool finds incorrect contacts or misses obvious ones
- New asset types: Emerging categories of digital assets we should support
- Integration requests: How you'd like to integrate this into your existing workflows
How to provide feedback:
- Community Discussion: disclose.io Discourse for general discussion and feature requests
- Technical Issues: Contact us via community.disclose.io for bug reports and technical feedback
The Bigger Picture
lookup.disclose.io addresses Problem #3 from the disclose.io mission: "There is no universal, vendor-agnostic way to determine whether an organization welcomes security research, what their legal posture is toward researchers, or how to contact their security team."
This tool embodies our core narrative that "vulnerability reporting is tricky by nature — every security issue is a snowflake, and the laws, languages, and people involved are unique every single time. disclose.io compensates for this by making secure easy and insecure obvious."
By automating security contact discovery, we remove friction from responsible disclosure and make it easier for researchers to do the right thing. Every successful vulnerability report that happens because the researcher could easily find the right contact is a win for Internet security.
Try It Now
Ready to see lookup.disclose.io in action?
- Web: Visit lookup.disclose.io and try searching for any asset
- MCP Integration: Connect to Claude Code or other MCP-compatible AI tools
We're excited to see how the community uses this tool and what improvements you suggest. Together, we can make security contact discovery as simple as it should have been all along.
lookup.disclose.io is a project of disclose.io, the open-source initiative for vulnerability disclosure standardization and safe harbor best practices.