Policy Pulse - Issue #10 | Week of April 14, 2026
Your weekly briefing on cybersecurity policy affecting vulnerability disclosure and security research.
Policy Pulse - Issue #10 | Week of April 14, 2026
Your weekly briefing on cybersecurity policy affecting vulnerability disclosure and security research.
Top Story
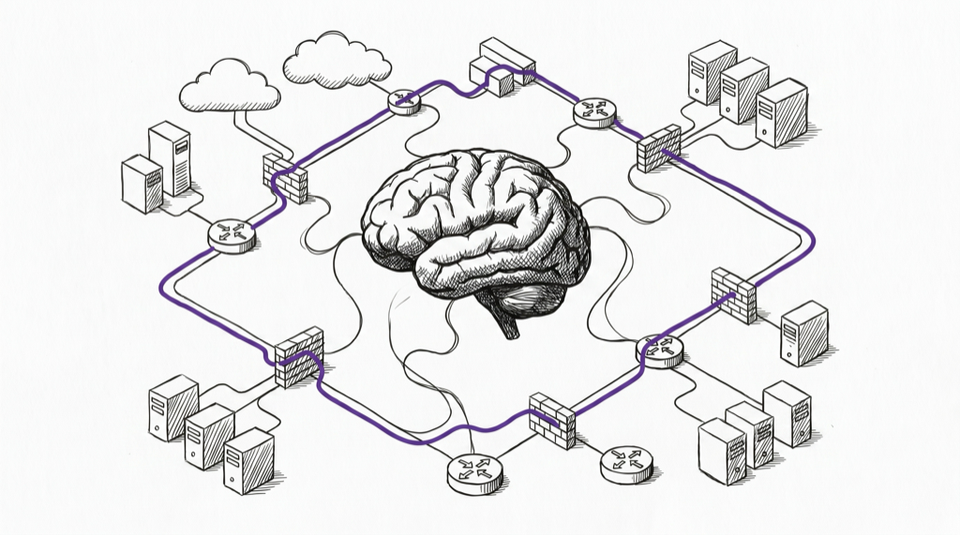
NIST AI Cybersecurity Framework Profile Working Sessions Signal Federal Governance Shift
NIST is conducting virtual working sessions to shape the Cybersecurity Framework Profile for Artificial Intelligence (Cyber AI Profile), representing the first federal attempt to systematically map CSF 2.0 controls to AI-specific risks. Unlike traditional vulnerability disclosure frameworks designed for deterministic software systems, this profile must address novel failure modes including prompt injection, tool misuse, and agentic goal hijacking that fundamentally alter how vulnerabilities manifest, propagate, and require remediation.
The working sessions focus on adapting cybersecurity practices to AI systems, strengthening technical content, and improving usability across different roles in the AI ecosystem. While the preliminary draft's public comment period has closed, ongoing working sessions provide opportunities for VDP practitioners to influence how AI vulnerability disclosure will be standardized across federal agencies and potentially adopted by industry.
Why it matters for VDP: Most vulnerability disclosure programs still treat AI endpoints like standard APIs, lacking taxonomies for AI-specific failure modes. This profile could establish the first federal guidance requiring VDP programs to develop AI-specific intake categories, modify triage procedures for prompt injection and model extraction attacks, and adapt remediation timelines for agentic systems where traditional patching may not apply.
Upcoming Deadlines & Events
| Date | Agency | Event/Deadline | Action Required | Link |
|---|---|---|---|---|
| April 24, 2026 | ED | Federal Student Aid GLBA Safeguards Compliance | Institutions in jurisdictions ≥50k population must comply | EDUCAUSE Guidance |
| May 6, 2026 | NIST | CSF 2.0 Informative References Quick-Start Guide | Public comment period closes | NIST CSRC |
| May 8, 2026 | NIST | SP 1800-42A Digital Identities/Mobile Driver's License | Public comment period closes | NIST Drafts |
| May 14, 2026 | NIST | Small Business Cybersecurity: Non-Employer Firms | Public comment period closes | NIST Drafts |
| May 2026 | CISA | CIRCIA Final Rule Publication Target | Monitor for 72-hour incident/24-hour ransom reporting requirements | CISA CIRCIA |
| June 12, 2026 | NIST | SP 800-230 Additional SLH-DSA Parameter Sets | Public comment period closes | NIST CSRC |
Note: CIRCIA finalization faces staffing constraints announced March 25, 2026. May target at risk of delay past mid-2026.
AI
WebGPU Vulnerability Exposes Browser-Based ML Inference Risk
CVE-2026-5281 in Google Dawn's WebGPU implementation demonstrates emerging attack surface in browser-based ML inference. The use-after-free vulnerability affects Chrome, Edge, and Opera, enabling arbitrary code execution after renderer compromise. Added to CISA's KEV catalog on April 1 with federal remediation deadline of April 15, this represents the only AI-adjacent vulnerability in April's KEV additions despite growing federal AI deployment.
Why it matters for VDP: Browser-based AI inference through WebGPU is increasingly common for privacy-sensitive applications. VDP programs need to expand scope definitions to include client-side ML infrastructure, not just traditional server-side AI services. The 14-day KEV remediation window may be insufficient for organizations with complex browser deployment policies affecting AI-enabled applications.
NIST AI RMF Profile for Critical Infrastructure Advances Federal AI Governance
NIST released a concept note guiding critical infrastructure operators toward specific risk management practices for AI-enabled capabilities (NIST). This profile complements the Cyber AI Profile working sessions, establishing parallel tracks for AI risk management and cybersecurity framework alignment.
Why it matters for VDP: Critical infrastructure AI deployments create cascading disclosure complexities when vulnerabilities affect both digital systems and physical operations. VDP programs serving critical infrastructure organizations need coordinated disclosure procedures that account for operational technology impact timelines, not just information technology patch cycles.
Federal
CISA Emergency Directive 26-03 Addresses Active SD-WAN Exploitation
Federal agencies must inventory Cisco SD-WAN systems, apply mitigations, and assess for compromise following active exploitation targeting privileged management access. The directive covers CVE-2026-20127 and CVE-2022-20775, with evidence of threat actors leveraging these vulnerabilities to gain persistent access to SD-WAN management components across federal networks (CISA).
Why it matters for VDP: SD-WAN infrastructure increasingly hosts edge AI processing capabilities for federal agencies. VDP programs need to understand network infrastructure dependencies when assessing AI system vulnerabilities, as compromise of underlying SD-WAN management can enable lateral movement to AI workloads without directly exploiting AI-specific vulnerabilities.
Strategic Consolidation: CISA Retires 10 Emergency Directives
In January 2026, CISA retired 10 emergency directives spanning 2019-2024, consolidating federal vulnerability management around the continuously updated KEV catalog (CISA). This represents a maturation from one-off emergency responses to systematized vulnerability prioritization through BOD 22-01's KEV framework.
Why it matters for VDP: The consolidation signals federal preference for persistent, data-driven vulnerability prioritization over reactive directives. VDP programs serving federal agencies should align reporting categories with KEV taxonomy and prepare for potential expansion of BOD 22-01 requirements to contractor networks and critical infrastructure partners.
CVE
April 2026 KEV Additions Reveal Perimeter-First Federal Attack Surface
Thirteen CVEs entered CISA's Known Exploited Vulnerabilities catalog in April 2026, with zero targeting AI/ML frameworks despite increased federal AI adoption. The additions cluster around perimeter appliances (Fortinet FortiClient EMS, Ivanti EPMM) and productivity software (Microsoft Office, Adobe Acrobat) rather than emerging technologies, indicating threat actors continue prioritizing established attack vectors over novel AI-specific techniques.
Critical 3-day deadlines: CVE-2026-21643 (Fortinet FortiClient EMS SQL injection, due April 16) and CVE-2026-1340 (Ivanti EPMM code injection, due April 11) received accelerated remediation timelines, signaling active federal network exploitation.
Why it matters for VDP: The absence of AI/ML CVEs in KEV additions suggests either insufficient AI vulnerability disclosure to warrant federal prioritization, or inadequate KEV taxonomy for AI-specific risks. VDP programs should prepare for potential KEV expansion to include AI vulnerability categories as federal AI deployment scales.
Legacy Vulnerability Resurgence Pattern
April KEV additions include CVE-2009-0238 (Microsoft Office Excel) and CVE-2012-1854 (Microsoft VBA), demonstrating threat actor exploitation of legacy vulnerabilities in current federal environments. These 14+ year old vulnerabilities received KEV inclusion due to fresh exploitation evidence, not initial discovery.
Why it matters for VDP: Long vulnerability lifecycles in federal environments mean disclosure programs must maintain institutional memory for decade-old vulnerabilities that remain exploitable. VDP programs should establish long-term tracking for vulnerabilities affecting federal systems, not just current-year discoveries.
Legal
DOJ Maintains CFAA Good Faith Research Policy Despite Reform Pressure
Despite continued advocacy for statutory protection, DOJ maintains its policy of not charging CFAA violations for legitimate security research, though legal experts note the limitations of prosecutorial discretion versus legislative protection (EFF). The policy continues to rely on case-by-case prosecutorial judgment rather than codified safe harbor provisions.
Why it matters for VDP: Prosecutorial discretion provides operational protection for VDP programs but creates legal uncertainty for researchers. Programs should maintain clear documentation of good faith research standards and coordinate with legal counsel when researchers test federal systems or critical infrastructure, where prosecutorial risk assessment may differ from commercial contexts.
Pall Mall Process Advances Commercial Cyber Intrusion Tool Governance
International efforts through the Pall Mall Process established guiding principles for states and industry regarding commercial cyber intrusion capabilities, with specific acknowledgment of benefits from good faith security research and bug bounties (France Diplomatie). The framework seeks to balance legitimate cybersecurity capabilities with preventing malicious exploitation.
Why it matters for VDP: International governance frameworks may affect vulnerability disclosure for security tools and capabilities marketed to government customers. VDP programs should understand potential regulatory constraints on research into commercial cybersecurity products, particularly those with dual-use applications in government and private sector contexts.
Worth Reading
- Coming in from the Cold: A Safe Harbor from the CFAA and DMCA §1201: Comprehensive analysis of needed statutory protections for security researchers beyond current prosecutorial guidance.
- Advancing Secure by Design Through Security Research: Policy framework connecting security research incentives to broader secure-by-design objectives.
- DOJ's Revised Prosecutorial Guidelines: The "Ethical" Hacker Exemption: Legal analysis of current DOJ policy limitations and recommendations for legislative action.
Policy Pulse is a weekly bulletin from disclose.io. Keeping the security research community informed on policy that affects our work.
Have a tip or want to contribute? Reply to this email, reach out on Twitter/X, or drop a comment here!