Policy Pulse - Issue #14 | Week of May 9, 2026
CAISI signs pre-deployment testing deals with Google, Microsoft, and xAI. CISA gives feds three days to patch Ivanti EPMM zero-day. NVD reclassifies 29,000 backlogged CVEs as Not Scheduled.
Policy Pulse - Issue #14 | Week of May 9, 2026
Your weekly briefing on cybersecurity policy affecting vulnerability disclosure and security research.
Top Story
Governments Line Up Behind Project Glasswing as Mythos Forces a New Disclosure Reality
Three weeks after Anthropic announced Claude Mythos Preview and the Project Glasswing consortium, policy reactions have emerged across multiple jurisdictions at unprecedented speed. The UK AI Security Institute (April 13) reported that Mythos completed its end-to-end 32-step "Last Ones" attack range in 3 of 10 runs and achieved 73% success on expert-level capture-the-flag exercises. Ireland's National Cyber Security Centre (April 13) endorsed the restricted-consortium approach, noting defenders currently maintain advantages and urging organizations to strengthen patch processes immediately. The UK Department for Science, Innovation and Technology and Cabinet Office jointly issued an open letter to business leaders (April 15, updated April 22) explicitly tying AI cyber-threat response to executive accountability, Cyber Essentials standards, and NCSC's Early Warning Service.
The critical structural element involves how Glasswing operates. Anthropic has granted Claude Mythos Preview access to AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks, and approximately 40 additional critical-software organizations, alongside $100 million in usage credits and $4 million directed toward open-source security initiatives. The model has already discovered thousands of zero-day vulnerabilities, with over 99% remaining unpatched at disclosure. This represents an immediate challenge rather than a future concern for vulnerability management queues. ProMarket has raised antitrust concerns regarding whether selective access to this defensive capability constitutes illegal restraint of trade under the Sherman Act, with the DOJ/FTC's February 2026 joint inquiry on competitor collaborations providing the regulatory framework likely to apply.
Why it matters for vulnerability disclosure programs: Traditional coordinated disclosure evolved for human-paced vulnerability discovery. The Glasswing model fundamentally changes this by granting a small number of vendors early access to AI-scale discovery capacity unavailable to public researchers, mid-market vendors, and downstream open-source maintainers. Organizations must reconsider triage backlogs, embargo windows, patch coordination across dependency chains, and initial notification protocols. If your program normally processes dozens of reports quarterly and operates within the dependency graph of a Glasswing partner organization, prepare for coordinated patch waves with timing outside your control.
Upcoming Deadlines & Events
| Date | Agency | Event/Deadline | Action Required | Link |
|---|---|---|---|---|
| May 10, 2026 | CISA / FCEB | CVE-2026-6973 (Ivanti EPMM RCE, KEV) remediation deadline | Patch FCEB systems to EPMM 12.6.1.1, 12.7.0.1, or 12.8.0.1; rotate Admin credentials | CISA KEV |
| May 15, 2026 | CISA | FCEB remediation deadline for CVE-2026-31431 (Linux kernel local privilege escalation, KEV) | Patch FCEB systems; non-FCEB organizations strongly advised to follow | CISA alert |
| May 19, 2026 | EU Commission | Feedback window on COM(2026) 11 EU Cybersecurity Act revision (post-publication consultation track) | Submit feedback if your vulnerability disclosure program involves EU certification or ENISA-coordinated disclosure | Have Your Say |
| September 11, 2026 | EU Commission | EU Cyber Resilience Act mandatory reporting of actively exploited vulnerabilities (24/72-hour windows) becomes binding | Stand up reporting workflows for products in scope; align vulnerability disclosure intake with CRA notification pathway | CRA reporting |
| December 11, 2027 | EU Commission | EU CRA full obligations (long-term security support, conformity assessment) take effect | Plan multi-year support windows into product vulnerability disclosure commitments | CRA timeline |
| TBD — May/June 2026 | CA Senate Appropriations | SB 898 — mandatory 5-year minimum support windows for connected consumer devices sold in California; currently in Appropriations Committee after May 5 amendment | Engage CA legislative staff if your connected devices sell in California; align support-window planning with parallel EU CRA commitments | SB 898 |
| Ongoing (review 2026) | UK Home Office | Computer Misuse Act statutory defence for security researchers, in active legislative drafting | Engage CyberUp consultation; track parliamentary progress | CyberUp Campaign |
The Ivanti EPMM deadline on May 10 is the most time-sensitive mandatory action this week, following CISA's 3-day patch window for the actively exploited zero-day. The Linux kernel KEV deadline (May 15) is the next near-term federal action. Five additional KEV entries from late April (PaperCut, JetBrains TeamCity, Kentico, Quest KACE, Synacor Zimbra, and three Cisco Catalyst SD-WAN flaws) have passed their deadlines; treat these as ongoing remediation rather than closed matters.
This Week in Policy
AI & Emerging Tech Security
Project Glasswing consortium expands beyond launch partners
Anthropic confirmed that access has extended to 40+ additional critical-software organizations beyond the original launch partners (AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks). The initiative includes $100 million in usage credits plus $4 million directed to open-source security work.
Why it matters for vulnerability disclosure: Open-source maintainers now participate in a frontier-model coordinated-disclosure arrangement for the first time. This precedent deserves protection and support.
CAISI signs pre-deployment testing agreements with Google DeepMind, Microsoft, and xAI
On May 5, 2026, NIST's Center for AI Standards and Innovation announced voluntary pre-deployment evaluation agreements with Google DeepMind, Microsoft, and xAI, covering national-security-relevant capabilities including cyber, biosecurity, and chemical-weapons risks. Models will be tested in classified environments with reduced or removed safeguards. The agreements build on earlier partnerships with OpenAI and Anthropic and are framed as the US government's most significant attempt yet to get ahead of security threats from powerful AI systems. (Cybersecurity Dive)
Why it matters for vulnerability disclosure: CAISI's testing framework creates a new channel through which AI capabilities are assessed for offensive cyber risk before public release. VDP programs should monitor CAISI evaluation reports for advance signal on capability classes that may arrive in public models within months.
UK AISI publishes first government evaluation of an offensive frontier-model cyber capability
The UK AI Security Institute released findings showing Mythos Preview achieved 73% success on expert-level capture-the-flag exercises and became the first model completing the 32-step "Last Ones" range end-to-end (3 of 10 runs).
Why it matters for vulnerability disclosure: AISI signaled that future evaluation cycles will employ active defenders and endpoint detection and response tools. This establishes a meaningful benchmark for assessing how much time blue teams actually gain.
AISI Frontier AI Trends Report quantifies the capability curve
AISI's inaugural Frontier AI Trends Report provides longitudinal data: AI models complete apprentice-level cyber tasks 50% of the time now, up from roughly 10% in early 2024. The length of tasks models can complete unassisted is doubling approximately every eight months, with no observed plateau as inference-time compute scales. On a 32-step enterprise network attack range, Claude Opus 4.6 (February 2026) averaged 15.6 steps, roughly 6 of the 14 hours a skilled human attacker requires. (AISI Report)
Why it matters for vulnerability disclosure: These benchmarks make the quantitative case that AI-discovered vulnerability volume is on an exponential curve. VDP programs without a concrete plan for AI-generated submission volume are behind.
Irish NCSC formally endorses the restricted-consortium model
Ireland's National Cyber Security Centre became the first EU-state national cyber authority publicly describing Glasswing-style limited release as "responsible."
Why it matters for vulnerability disclosure: EU regulator endorsement of asymmetric early access now appears on the record, likely to be cited in Cyber Resilience Act and Cybersecurity Act revision deliberations.
UK joint open letter from DSIT and Cabinet Office to business leaders on AI cyber threats
Signed by Liz Kendall and Dan Jarvis MBE (April 15, updated April 22), the letter anchors response frameworks to Cyber Essentials, the Cyber Governance Code of Practice, and the NCSC Early Warning Service.
Why it matters for vulnerability disclosure: The UK government has positioned AI cyber risk as a board-level governance matter rather than a chief information security officer line item. This reframes vulnerability disclosure funding and executive prioritization within large UK enterprises.
NCSC publishes position paper: why cyber defenders need to be ready for frontier AI
The UK National Cyber Security Centre issued guidance confirming AI can meaningfully augment defensive security operations, while reinforcing that basic cyber hygiene is the prerequisite. (NCSC)
Why it matters for vulnerability disclosure: NCSC's endorsement of AI-assisted defence normalizes using AI tooling in disclosure triage and researcher-facing automation, supporting the case for AI-assisted VDP coordination as a legitimate security function.
Antitrust scrutiny of Glasswing emerges
ProMarket argues that the consortium's information-sharing protocols and exclusion of non-members may violate Sherman Act provisions; the DOJ/FTC's February 2026 joint inquiry on competitor collaborations represents the regulatory lens likely to apply.
Why it matters for vulnerability disclosure: If antitrust regulators mandate broader access, vulnerability disclosure coordinators currently outside Glasswing may suddenly find themselves included. Watch for the first FTC business-review letter request.
Federal Strategy & Regulation
CISA adds Ivanti EPMM zero-day to KEV with 3-day federal remediation window
On May 7, CISA added CVE-2026-6973 to the Known Exploited Vulnerabilities catalog: an authenticated remote code execution vulnerability in Ivanti Endpoint Manager Mobile (CVSS 7.2) being actively exploited against exposed instances. Shadowserver tracked over 800 internet-exposed EPMM appliances as of that date. Federal agencies face a May 10 remediation deadline (3 days from addition). Ivanti's advisory links the flaw to prior credential compromise via CVE-2026-1281 and CVE-2026-1340. (Bleeping Computer)
Why it matters for vulnerability disclosure: Repeated Ivanti KEV entries form a pattern: enterprise mobility management is a systematic target class. VDP programs at organizations running MDM infrastructure should reassess scope language and researcher incentives for this category.
American Leadership in AI Act introduced
Representatives Lieu (D-CA-36) and Obernolte (R-CA-23) introduced a consolidated bipartisan package combining 20+ prior AI proposals across six titles, including federal AI procurement security and AI-incident tracking. The legislation incorporates Representative Ross's AI Incident Reporting and Security Enhancement Act, directing NIST to add AI systems to the National Vulnerability Database and establish a federal AI vulnerability reporting process coordinated with CISA.
Why it matters for vulnerability disclosure: Adding AI systems to the NVD represents the structural change vulnerability disclosure practitioners have requested. Advancing this through an omnibus AI bill rather than standalone legislation likely accelerates passage.
California SB 898 — connected consumer products face mandatory 5-year support windows
California SB 898 amends the state's Unfair Competition Law to require manufacturers of internet-connected consumer devices to disclose a guaranteed minimum five-year support period before purchase and prohibit retroactive reduction of that commitment. Manufacturers must provide public notice when products reach end-of-life. Businesses leasing connected devices face additional obligations: prompt update application and no-cost end-of-life device replacement with comparable alternatives. The bill passed Senate Judiciary on April 21, was amended, and was re-referred to the Senate Appropriations Committee on May 5. (CalMatters Digital Democracy)
Why it matters for vulnerability disclosure: SB 898 is the US state-level equivalent of the EU Cyber Resilience Act's long-term security support requirements, grounded in California's Unfair Competition Law rather than product regulation. VDP programs covering connected consumer devices sold in California would face a statutory floor: five years of support minimum from point of sale. Combined with the CRA's December 2027 deadline for EU markets, connected-device vendors now face converging multi-jurisdiction support-window mandates. If your program covers IoT or connected consumer hardware, this bill should be shaping your disclosure policy commitments now, not at end-of-life.
CISA adds CVE-2026-31431 (Linux kernel) to KEV
A local privilege escalation vulnerability with active exploitation has been added to CISA's Known Exploited Vulnerabilities catalog; the FCEB remediation deadline is May 15. This continues the pattern from late April, which saw eight KEV additions including Cisco Catalyst SD-WAN, PaperCut, JetBrains TeamCity, Kentico, Quest KACE, and Synacor Zimbra entries.
Why it matters for vulnerability disclosure: Linux-kernel KEV additions signal that downstream Linux distribution vulnerability disclosure coordination requires airtight processes. Organizations shipping Linux as appliance components must ensure federal customer compliance depends on reliable patch timelines.
CVE & Vulnerability Programs
NVD adopts risk-based enrichment model, abandons 29,000 backlogged CVEs
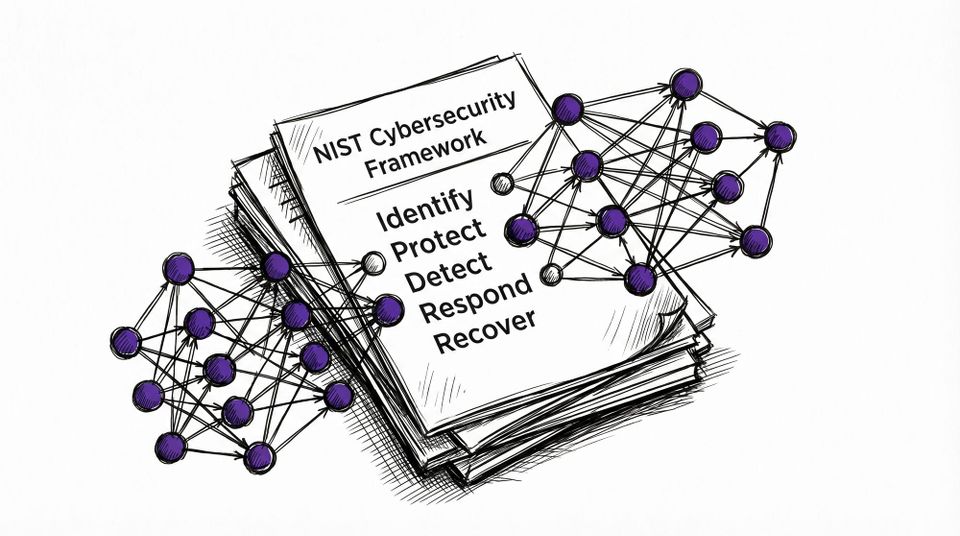
On April 15, NIST confirmed the National Vulnerability Database will no longer enrich approximately 29,000 CVEs with publish dates before March 1, 2026, reclassifying them as "Not Scheduled." The trigger: a 263% surge in CVE submission volume since 2020 exceeded analytical capacity. Going forward, NVD prioritizes enrichment for CVEs in federal-agency software, EO 14028 critical software, and CISA KEV entries. Everything else waits indefinitely. The visible backlog dropped from over 33,000 entries to roughly 4,000, not by solving the problem but by reclassifying it. (NIST)
Why it matters for vulnerability disclosure: Any triage automation that reads CVSS scores from NVD is now working from an incomplete dataset. VDP programs should audit their scoring pipelines and add KEV membership and federal software presence as explicit enrichment signals alongside CVSS.
CVE program funding stable, CVE Foundation operational
Following the April 2025 funding crisis, CISA's 11-month MITRE extension combined with the new CVE Foundation non-profit structure has produced a functioning dual framework. ENISA's European Vulnerability Database remains in beta as the EU's parallel initiative.
Why it matters for vulnerability disclosure: The CVE Foundation's existence prevents any single US administration from unilaterally discontinuing the CVE program. This represents the structural safeguard the security community sought.
Legal & Researcher Protections
UK Computer Misuse Act statutory defence still in active drafting
Security Minister Dan Jarvis confirmed in December 2025 that the government is pursuing a Computer Misuse Act statutory defence for security researchers. CyberUp's April 16 report positions the UK behind the US, France, and Australia on researcher protection benchmarks. No bill text has emerged in 2026.
Why it matters for vulnerability disclosure: UK researchers currently operate without statutory protection. Every month without legislative progress increases vulnerability for independent finders operating in the post-Mythos environment.
CFAA good-faith policy remains unchanged from 2022 DOJ guidance
No legislative movement this week; the policy remains binding on prosecutors rather than courts and provides no defence against private civil actions.
Why it matters for vulnerability disclosure: Researchers relying on DOJ good-faith carve-out protection require explicit safe-harbor language within program scopes. Policy guidance cannot substitute for contractual protection.
International Developments
EU Cybersecurity Act revision (COM(2026) 11) consultation track active
Published January 20, 2026, the revision proposes ICT supply-chain security enhancements, simplified certification, and strengthened ENISA mandate. The feedback channel remains open through the "Have Your Say" portal until May 19.
Why it matters for vulnerability disclosure: ENISA represents the EU's closest equivalent to a coordinated-disclosure focal point. Expanding its mandate directly addresses vulnerability disclosure infrastructure needs.
UN Cybercrime Treaty: no movement until January 2027
Vienna talks in January 2026 failed to achieve procedural consensus; no additional sessions are scheduled before 2027.
Why it matters for vulnerability disclosure: Researcher-protection language within the treaty remains unresolved. The twelve-month interval provides a window for civil-society advocacy regarding carve-outs for good-faith security research.
Friends of disclose.io
CyberUp Campaign: "Cybersecurity at a Crossroads" (April 16, 2026)
The CyberUp Campaign pursues a single objective: updating the UK's Computer Misuse Act 1990 to ensure good-faith security research is not prosecuted as criminal conduct. Their April 16 report, "Cybersecurity at a Crossroads," represents the campaign's most compelling policy argument to date, arriving at precisely the right moment. With Project Glasswing distributing AI-scale vulnerability discovery to a restricted group, the gap between protected and unprotected finders has shifted from a legal-hygiene question to a structural question about who participates in vulnerability discovery itself.
The report demonstrates, with comparative evidence, that the UK now lags the US, France, and Australia on legal protections for cybersecurity professionals, with this gap suppressing UK cyber innovation, resilience, and talent retention. Security Minister Dan Jarvis confirmed in December 2025 that the government is exploring a Computer Misuse Act statutory defence; CyberUp's framework (which conditions the defence on harm-versus-benefit analysis, proportionality, intent, and competence) remains the leading legislative proposal. February 2026 saw amendments to the Cyber Security and Resilience Bill withdrawn following ministerial reassurances. The government's next action will be decisive.
Key findings:
- UK legal protections for security researchers lag the US, France, and Australia
- The existing Computer Misuse Act framework jeopardizes UK cyber innovation, resilience, and talent retention
- A statutory defence framework (incorporating harm-versus-benefit, proportionality, intent, and competence) stands ready for legislative development
- Ministerial commitment exists; enacted legislation does not yet
Read the full report and join the campaign
CyberUp represents the most systematic, sustained researcher-protection campaign in the UK. In a post-Mythos environment where governments are publicly determining who receives defensive capabilities first, protecting independent vulnerability discoverers is no longer an aspirational goal — it represents a structural necessity. disclose.io affirms its support for CyberUp.
Worth Reading
-
Project Glasswing: Securing critical software for the AI era (Anthropic): The primary source document. Review this before additional sources.
-
Our evaluation of Claude Mythos Preview's cyber capabilities (UK AISI): The first government-published offensive cyber assessment of a frontier model. Include this in vulnerability and AI risk assessments.
-
AISI Frontier AI Trends Report (UK AISI): Longitudinal quantification of the AI cyber capability curve across 18 months and seven frontier models. The data behind the policy coverage.
-
The Antitrust Risks of Anthropic's Project Glasswing and the 'AI Avengers' (ProMarket, Madhavi Singh): A substantive legal counterargument to selective consortium access, framed as a Sherman Act concern rather than a values-based critique.
-
On Anthropic's Mythos Preview and Project Glasswing (Bruce Schneier): Schneier's analysis emphasizes that the asymmetry between defenders with Mythos access and others without it matters more than the model's capabilities themselves.
-
NCSC statement on Anthropic's Mythos Preview (Ireland NCSC): First EU national cyber authority public statement. Concise and direct.
-
NIST will test three major tech firms' frontier AI models for cybersecurity risks (Cybersecurity Dive): Good explainer on the CAISI pre-deployment testing agreements and what classified model evaluation means in practice.
Policy Pulse is a weekly briefing from disclose.io. We keep the security research community informed about policy affecting vulnerability disclosure and security research.
Have information to contribute or want to participate? Reply to this email, contact us on Twitter/X or Bluesky (@disclose_io), or comment on community.disclose.io.