Policy Pulse - Issue #12 | Week of April 26, 2026
CISA's KEV catalog absorbs 13 new CVEs in five days, the heaviest week since Emergency Directives retired in January. UK AISI publishes the first government evaluation of a frontier model's offensive cyber capabilities.
Your weekly briefing on cybersecurity policy affecting vulnerability disclosure and security research.
Top Story
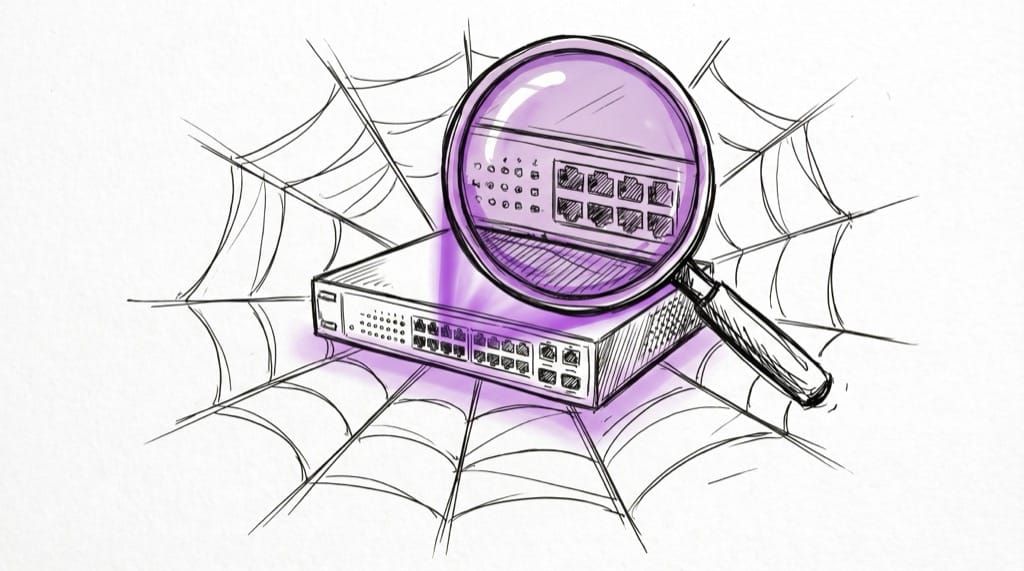
CISA's KEV Catalog Absorbs 13 New CVEs in Five Days as the Post-Emergency-Directive Era Goes Live
In the week of April 20-24, CISA pushed thirteen new vulnerabilities into the Known Exploited Vulnerabilities catalog across three batches, the heaviest single-week cadence since the agency retired ten Emergency Directives in January in favor of the KEV catalog as the primary federal remediation lever. April 20's batch of eight CVEs included three Cisco Catalyst SD-WAN Manager flaws (CVE-2026-20122, CVE-2026-20128, CVE-2026-20133) layered on top of the standing ED 26-03 coverage of CVE-2026-20127 (CVSS 10.0, authentication bypass exploited since 2023), alongside PaperCut, JetBrains TeamCity, Kentico Xperience, Quest KACE, and Synacor Zimbra. April 22 added a single Microsoft Defender access-control flaw (CVE-2026-33825), and April 24 added four more covering Samsung MagicINFO, two SimpleHelp authorization bugs, and a D-Link DIR-823X command injection.
The cadence is the story. CISA's January retirement of bulk-issued EDs implicitly bet that the KEV catalog plus BOD 22-01 timelines could absorb the operational role those directives used to play. This week is the first stress test at scale, and it lands while CISA is also coordinating a Five Eyes joint advisory on the underlying Cisco SD-WAN exploitation campaign with NCSC-UK, ASD, CCCS, and NCSC-NZ. Significantly, half of the April 24 entries (SimpleHelp, D-Link DIR-823X) are small-vendor and consumer-router products that historically struggle to get federal mitigation attention.
Why it matters for VDP: Coordinated disclosure programs benefit asymmetrically when KEV is doing the operational work that EDs used to do, because KEV is the artifact that drives downstream agency triage, ISAC sharing, and procurement risk reviews. VDP teams at small-vendor or consumer-IoT companies should specifically watch the SimpleHelp and D-Link entries as evidence that the catalog is finally scaling beyond enterprise software, which means inbound reports against those product classes are about to carry more weight in your queue.
Throwback: In Issue #11, we covered how CIRCIA's funding lapse was rerouting CISA's operational tempo. This week's KEV burst is what that rerouted tempo looks like when the catalog has to carry the load.
Upcoming Deadlines & Events
| Date | Agency | Event/Deadline | Action Required | Link |
|---|---|---|---|---|
| Apr 30, 2026 | ENISA | EU Digital Identity Wallet certification consultation closes | Submit comment | enisa.europa.eu |
| Rolling | CISA | ED 26-03 ongoing Hunt and Hardening for Cisco SD-WAN | Continue Cisco SD-WAN Manager forensic hunt per Supplemental Direction | cisa.gov |
| May 1, 2026 | DEF CON | DC34 Policy / Workshops / Demo Labs CFPs close | Submit talks, workshops, labs | defcon.org |
| May 6, 2026 | NIST CSRC | CSF 2.0 Quick-Start Guide comments close | Submit comment | csrc.nist.gov |
| May 15, 2026 | ONCD | FOIA and Privacy Act regs comment close | Submit comment | federalregister.gov |
| Jun 15, 2026 | TSA | Cybersecurity Measures for Surface Modes comments close | Submit comment | federalregister.gov |
| Sep 11, 2026 | EC | EU Cyber Resilience Act vulnerability reporting begins | Register CSIRT contact, prep 24/72-hour reporting | digital-strategy.ec.europa.eu |
| Sep 30, 2026 | Congress | CISA 2015 information sharing reauthorization sunsets | Plan for liability protection lapse if no extension | congress.gov |
This Week in Policy
AI & Emerging Tech Security
-
UK AISI publishes first government evaluation of a frontier model's offensive cyber capabilities: AISI's April 14 evaluation of Claude Mythos Preview is the most concrete government output to date on a specific frontier model's offensive-cyber profile. Mythos became the first model to complete AISI's "The Last Ones" 32-step network-takeover range — a workflow estimated at roughly 20 hours for human experts — while Claude Opus 4.6, the next-best model tested, averaged 16 of 32 steps. AISI flagged hard caveats: its ranges lack live defenders, EDR, or real-time incident response, and Mythos failed the OT-focused "Cooling Tower" range (getting stuck on IT-layer sections rather than ICS controls). The Bank of England's Cross Market Operational Resilience Group is briefing UK bank and insurance CEOs within two weeks of the release — first sector-regulator follow-through anywhere. Why it matters for VDP: program teams sitting outside Anthropic's Project Glasswing partner set (Amazon, Apple, Broadcom, Cisco, CrowdStrike, Linux Foundation, Microsoft, Palo Alto Networks, plus ~30 more) are downstream of whatever briefing cascade those vendors choose to run; intake processes should expect AI-scale submission volume well before formal regulatory cover lands.
-
Microsoft ships Agent Governance Toolkit covering all 10 OWASP agentic risks: Microsoft's open-source Agent Governance Toolkit released April 2 is the first runtime stack to claim coverage of every OWASP Agentic Top 10 risk, with sub-millisecond policy enforcement (p99 < 0.1ms), DID-based agent identity, and an Agent Marketplace that gates plugins via Ed25519 signing. Why it matters for VDP: this gives disclosure programs an actual reference target when reports describe agent-level supply chain or policy-bypass bugs; expect "but does it block this in Microsoft AGT?" to become a triage shorthand. (Microsoft / GitHub)
-
NIST CAISI Agent Identity RFI window closed April 2: The NCCoE concept paper on AI Agent Identity and Authorization closed comments April 2 and is the most operationally relevant NIST artifact for enterprise teams trying to map existing IAM standards onto agent populations. Why it matters for VDP: once NIST publishes the response document, expect program scope and authentication boundaries in agentic VDP submissions to shift toward whatever identity model the final guidance endorses. (NIST CAISI)
-
CAISI sector listening sessions running through April: CAISI is holding sector-specific virtual listening sessions on AI agent adoption barriers across financial services, healthcare, and education, feeding directly into 2026 sector guidance. Why it matters for VDP: sector-specific outcomes almost always carry security expectations that VDP scope statements will need to mirror, particularly for healthcare. (Pillsbury Law summary)
Federal Strategy & Regulation
-
CISA does not have access to Mythos; US policy reaction still pre-formal: Axios reported April 21 that CISA was briefed in advance on Mythos's offensive and defensive capabilities but has not been given access to the model itself, and the agency has not issued formal guidance on AI-discovered vulnerabilities. CISA's existing artifacts — BOD 20-01 and the VDP template — were built for human-researcher disclosure cadence, not AI-scale discovery. VP Vance and Treasury Secretary Bessent questioned tech giants on AI security ahead of the Mythos announcement, and Mythos has drawn explicit White House attention, but no Mythos-specific EO, NSPM, or congressional bill exists yet. Why it matters for VDP: the first US policy artifact for this class of capability is most likely to come through NIST CAISI's voluntary pre-deployment frontier-model testing — already chartered under the March 2026 AI Policy Framework — rather than via CISA guidance or new legislation; programs should track CAISI's output channel rather than waiting on a CISA directive.
-
Trump cyber strategy and cybercrime EO continue to drive April policy work: President Trump's Cyber Strategy for America and the accompanying Executive Order on cyber-enabled crime, both released March 6, remain in active interagency implementation, with an action plan against transnational criminal organizations directed in the EO. The strategy explicitly pledges to avoid "costly checklist[s]" and streamline cyber regulations. Why it matters for VDP: the deregulatory tone telegraphs lighter federal compliance asks but heavier emphasis on private-sector partnership, which historically translates into more weight on industry VDP frameworks rather than top-down mandates. (Latham & Watkins analysis)
-
CISA 2015 sunset clock now 5 months out: The reauthorization passed in the February 3 funding bill only extended CISA 2015 through September 30, 2026, without amending substance. Why it matters for VDP: many vendor disclosure pipelines lean on CISA 2015's liability protections when sharing inbound reports laterally with CISA or ISACs; if September passes without action, programs will need new sharing posture overnight.
CVE & Vulnerability Programs
-
April 2026 KEV adds reach 23+ entries across four batches: CISA added eight CVEs on April 20 (PaperCut, JetBrains TeamCity, Kentico Xperience, Quest KACE, Synacor Zimbra, three Cisco SD-WAN Manager), one on April 22 (Microsoft Defender CVE-2026-33825), and four on April 24 (Samsung MagicINFO, two SimpleHelp, D-Link DIR-823X). Why it matters for VDP: the SimpleHelp and D-Link entries in particular validate small-vendor and consumer-router disclosure pathways that often go un-triaged; pointing internal stakeholders at the KEV provenance is the cheapest way to get attention.
-
Qualys RSAC study: half of weaponized vulns exploited before disclosure: At RSAC 2026, Qualys TRU released a 1B-record KEV remediation study spanning 10,000 organizations and four years, finding vulnerability volume up 6.5x in three years and that 26 of 52 weaponized CVEs were exploited before public disclosure (median exploitation timeline: -1 days). Why it matters for VDP: this is fresh quantitative ammunition for arguing that coordinated-disclosure-with-embargo still beats race-to-CVE; share this with vendors who push for "publish on patch."
Legal & Researcher Protections
- UK Crime and Policing Bill went to Lords-amendments stage April 14, but CMA statutory defence still missing: The Commons considered Lords amendments on April 14 without picking up the CyberUp-backed statutory defence, despite the Home Office's standing pledge to reform the Computer Misuse Act 1990. At CYBERUK 2026, CyberUp again named Portugal, France, Germany, Australia, and the US as peers that have already modernized. Why it matters for VDP: UK-domiciled researchers remain the only Five Eyes practitioners still operating without an explicit statutory good-faith defence; vendors running global VDPs should flag UK-specific intake risk in their counsel briefings.
International Developments
-
Australia ransomware reporting moves to Phase 2 enforcement on January 1, 2026: Phase 2 of Australia's mandatory ransomware payment reporting shifted Home Affairs from education to active oversight as of the new year, with civil penalties up to 60 penalty units (~AUD 19,800) for missed 72-hour reports for entities over AUD 3M turnover or any SOCI critical-infrastructure operator. Why it matters for VDP: Australian disclosure programs intersecting incident response now need a documented reporting hand-off path, since ransomware events can start as inbound bug reports.
-
New Zealand Cyber Security Strategy 2026–2030 critical-infrastructure consultation closed April 19: Comments closed April 19 on the NZ Government's consultation on enhancing the cybersecurity of New Zealand's critical infrastructure, which sits inside the broader Cyber Security Strategy 2026–2030 and its accompanying Action Plan. Industry submissions, including from the Hacking Policy Council, urged the NZ Government to (1) recognize VDPs and AI red-teaming as baseline risk-management tools for critical infrastructure, (2) establish explicit legal safeguards for good-faith cybersecurity research, and (3) avoid mandates that force premature sharing of unmitigated vulnerabilities before mitigations and secure handling channels exist. Why it matters for VDP: if NZ lands on a Five-Eyes-style baseline expectation that critical-infrastructure operators run a VDP, that becomes a clean external citation outside the EU CRA for vendor counsel pushing internally for default VDP coverage of CI products; the premature-disclosure point is the one to flag in every CI incident-reporting regime conversation globally right now.
-
Japan publishes Guidelines on the Roles Expected of Cyber Infrastructure Providers: A new Japanese policy framework, Guidelines on the Roles Expected of Cyber Infrastructure Providers, lays out a shared-responsibility model for vulnerability management across developers, suppliers, operators, and customers throughout the product lifecycle. The guidelines instruct providers to "arrange vulnerability disclosure policies" and stand up formal vulnerability response systems (severity assessment, remediation, stakeholder communication), embed secure-by-design and secure-by-default expectations from the development phase, encourage SBOM adoption to extend visibility into third-party dependencies, and place explicit procurement-side responsibility on critical-infrastructure customers to evaluate provider security practices — including their approach to vulnerability management and disclosure — as part of buying decisions. Why it matters for VDP: this is the most explicit alignment with coordinated vulnerability disclosure principles Japan has taken in policy to date, and the customer-procurement framing is the part that will move first in practice. Vendors selling into the Japanese CI market should fast-track documented VDP posture and SBOM availability before customer security questionnaires start citing the guidelines back at them.
-
EU CRA delegated act on CSIRT delay published; September 11 reporting still on: The Commission has adopted a Delegated Act letting CSIRTs justifiably delay onward dissemination of vulnerability notifications, and March 2026 draft guidance has now been published to help manufacturers operationalize the 24/72-hour and 14-day reporting windows that go live September 11. Why it matters for VDP: EU-active vendors should confirm their disclosure intake forms have a "report goes to CSIRT" branch ready, and that program counsel understands when CSIRTs can hold a vulnerability close.
-
Pall Mall Process voluntary code keeps gathering signatories: The Pall Mall Process, the UK/France-led voluntary code on commercial cyber intrusion capabilities, continues to accumulate state and industry signatories around its four pillars (accountability, precision, transparency, oversight). Why it matters for VDP: Pall Mall is the closest thing to a normative answer to "where does coordinated vulnerability disclosure end and offensive enablement begin?" for spyware-adjacent vendors.
Worth Reading
-
Our evaluation of Claude Mythos Preview's cyber capabilities (UK AI Security Institute): The single most rigorous public artifact on a frontier model's offensive cyber profile. Worth reading alongside AISI's caveats on weakly-defended-system framing before extrapolating to live, defended environments.
-
Patching the CFAA so Researchers No Longer Pay (Cybaris, Mitchell Hamline): Argues the post-Van Buren landscape still leaves civil-side CFAA exposure intact and proposes a statutory "good faith" definition with the cleanest legislative fingerprint of any current US proposal.
-
A Safe Harbor for AI Evaluation and Red Teaming (Knight First Amendment Institute): The foundational case for legal+technical safe harbor for AI evaluators; useful for briefing leadership on what a VDP-style safe harbor looks like applied to AI systems.
-
The Pall Mall Process on Cyber Intrusion Capabilities (Lawfare): Best single explainer of how Pall Mall sits next to (and sometimes against) the UN Cybercrime Convention and Budapest Convention frames.
-
CISA Closes 10 Emergency Directives as Vulnerability Catalog Takes Over (SecurityWeek): Useful context for ED 26-03 above, framing why this directive lands differently than past ones.
-
NIST's AI Agent Standards Initiative: Why Autonomous AI Just Became Washington's Problem (Jones Walker): Strong policy framing for the agentic-AI compliance story, with practical hooks for program teams.
Friends of disclose.io
Microsoft Open Source: Agent Governance Toolkit
Microsoft's release of the Agent Governance Toolkit on April 2 is one of the more meaningful infrastructure drops the agentic-AI security ecosystem has seen this year, because it gives VDP teams a concrete artifact to triage against rather than another policy document. It is also the first toolkit claiming explicit coverage of all ten OWASP Agentic Top 10 categories with deterministic, sub-millisecond runtime enforcement.
The toolkit ships five components: Agent OS (sub-millisecond policy engine), Agent Mesh (DID-based identity plus behavioral trust scoring), Agent Compliance (auto-mapped to EU AI Act, HIPAA, SOC2), Agent Marketplace (Ed25519-signed plugin lifecycle), and Agent Lightning (RL training under policy). Each plugs into LangChain callbacks, CrewAI task decorators, Google ADK plugins, and the Microsoft Agent Framework middleware pipeline, so programs do not need to demand framework migration to start using the controls.
Key findings:
- First toolkit to claim full OWASP Agentic Top 10 coverage with runtime enforcement
- p99 latency under 0.1ms makes inline policy evaluation tractable for production agents
- DID-based identity gives VDP programs a meaningful authentication boundary to scope reports against
- Compliance grading auto-maps to EU AI Act, HIPAA, and SOC2 evidence collection
Read the Microsoft Open Source post | Repo
Microsoft's open-source security tooling has historically run several years ahead of the policy artifacts that eventually ratify it; AGT is worth watching as both a real defensive control surface and a likely template for future agentic security mandates.
Policy Pulse is a weekly bulletin from disclose.io. Keeping the security research community informed on policy that affects our work.
Have a tip or want to contribute? Reply to this email, reach out on Twitter/X, or drop a comment here!